AI Articles
AccelQ Codeless Test Automation Tool
In today’s fast-paced software development environment, the need for efficient, reliable, and scalable testing solutions is important. Traditional testing methods often struggle to keep up
What is Forward Chaining in AI?
Forward chaining in AI is an example of the general concept of data-driven reasoning – i.e., reasoning in which the focus of attention starts with
Character AI | Explore Every Moment of Your Day
In today’s fast-paced digital world, personalized interactions are key to enhancing user experiences. Enter Character AI, a groundbreaking platform that leverages advanced artificial intelligence to

How Janitor AI Brings Characters to Life
Chatbots have become integral to our digital landscape, driving everything from customer service to virtual companionship. Amid this growing reliance on automated interactions, Janitor AI

Remaker AI Face Swap Tool
Table of Contents What is Remaker AI? Remaker AI is an innovative face swap tool that utilizes artificial intelligence to seamlessly replace faces in images

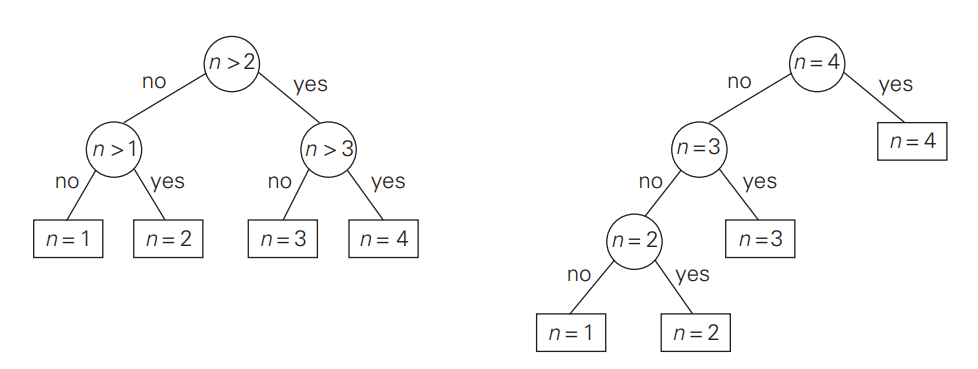
Learn Alpha Beta Pruning in AI – Boost Your Game Development
Introduction Alpha Beta Pruning in AI is a search algorithm that reduces the number of nodes evaluated in the minimax algorithm in game theory and
Amazon CodeWhisperer vs GitHub Copilot Comparison
In the fast-evolving landscape of AI-powered coding assistants, Amazon CodeWhisperer vs Copilot stand out as revolutionary tools designed to optimize the coding process. This article

ClipDrop AI Image Generator | Best Visual Creation Tool
The ClipDrop AI Image generator is an all-in-one video AI platform designed to revolutionize how creators produce eye-catching visuals. In the dynamic realm of digital
Algorithm
Sponsor
Explore
Technology Articles

Top 30 Software Testing Interview Questions (2024)
Software testing is a procedure used in the software development life-cycle to confirm that the program is accurate and functions

Top 30 Essential Microservices Interview Questions
Table of Contents Navigating the complex world of microservices can be a difficult journey, especially when you’re standing outside the
Top 30 Best React Native Interview Questions (2024)
Are you gearing up for a career in React Native development? Whether you’re a seasoned developer or just starting out,

Top 10 Best 55 Inch Smart TV in India
Table of Contents Investing in a best 55 inch smart TV in India can significantly enhance your home entertainment experience,

Top 20 Best Digital Marketing Interview Questions (2024)
Table of Contents Digital marketing is a dynamic field that requires up-to-date knowledge of technology, market trends, and effective communication

30 Best Terraform Interview Questions to Master!
Prepare for your next job interview with our comprehensive guide to the Top Terraform Interview Questions. Whether you’re a beginner